Last week’s Pioneer Awards were absolutely amazing. I will be posting video soon, but here are some photos.
Come to this year’s Aaron Swartz Day evening event!





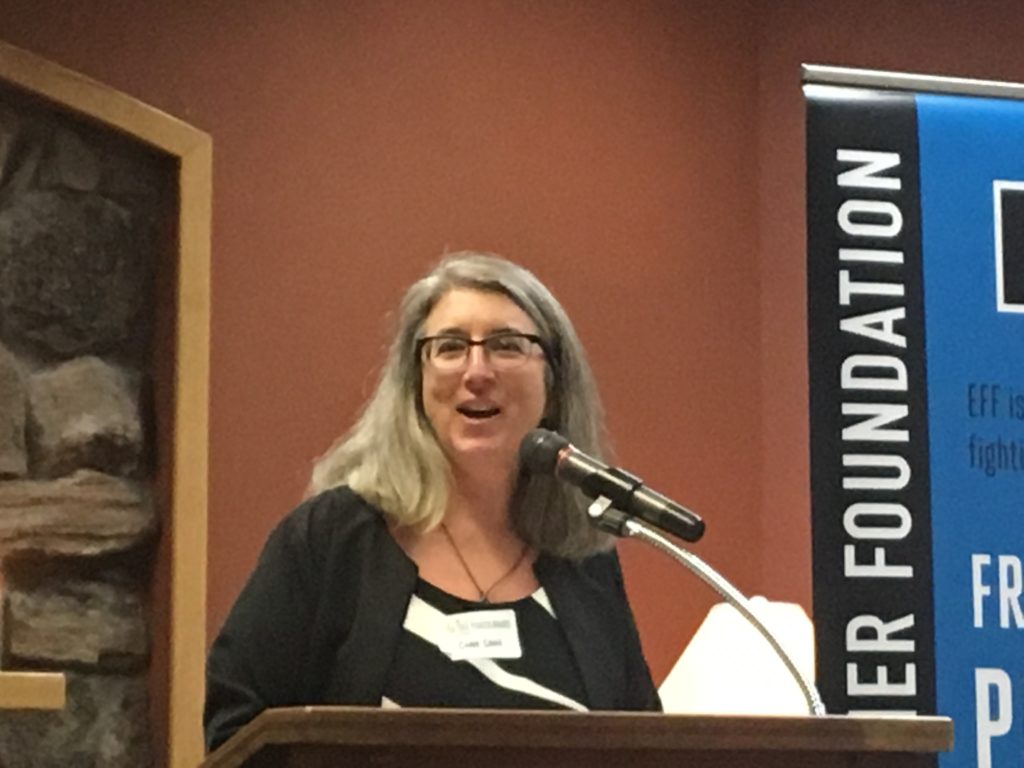

Last week’s Pioneer Awards were absolutely amazing. I will be posting video soon, but here are some photos.
Come to this year’s Aaron Swartz Day evening event!






See Caroline Sinders at this year’s Aaron Swartz Day International Hackathon, at the San Francisco Hackathon‘s Ethical Algorithm Panel, Saturday at 2pm, and at the evening event, Saturday night, November 4, 7:30 pm.
8 AI Designers That You Need To Know by Adelyn Zhou for Forbes.
Caroline Sinders – Machine Learning Designer and Researcher, former Interaction Designer for IBM Watson
Caroline Sinders
Caroline is an artist, designer, and activist who also loves writing codes. She helped design and market IBM Watson, a billion-dollar artificial intelligence system built on advanced natural language processing, automated reasoning, machine learning, and other technologies. Sinders’ work on Watson focused on user flows and the impact of human decision-making in the development of robotics software. She recently left her dream job at IBM to pursue an equally challenging fellowship at Open Labs. A passionate crusader against online harassment, Caroline probes the different ways design can influence and shape digital conversations, with the ultimate goal of using machine learning to address online harassment. You can weigh her strong opinions on Twitter, Medium, LinkedIn, and her personal website.
Hackathons are being planned for November 4th in San Francisco, New York, and even Cairo!
So far, the projects are the Freedom of the Press Foundation’s SecureDrop and these topics:
Send an email to lisa@lisarein.com if you are planning a hackathon :-)
We are putting together new “Hackathon 101” materials too!
So, if you have good “how to have a hackathon” resources, please email them too! :-)
Seems like a good time for a reminder. (This content is from our “Setting the Record Straight” page that has been up since October 2014.)
FACT: Aaron implemented a piece of software that downloaded articles from the JSTOR website faster than JSTOR originally intended. Aaron’s software downloaded articles from the JSTOR website to Aaron’s laptop, just like a live person would have downloaded them, but without his having to sit there and click through each of the steps manually. Source: Alex Stamos, http://unhandled.com/2013/01/12/the-truth-about-aaron-swartzs-crime/
FACT: Aaron did not hack into any of MIT’s computers. The CFAA requires that a person gain access to a computer that they weren’t authorized to access. Aaron was obviously authorized to access his own laptop.
FACT: Aaron did not hack into MIT’s network. Aaron connected his laptop to MIT’s open network by walking into an open computer closet on MITs open campus and simply plugging into an unused ethernet port. Source: Alex Stamos, http://unhandled.com/2013/01/12/the-truth-about-aaron-swartzs-crime/
FACT: Aaron was a “Fellow” at the Harvard University Edmond J. Safra Center for Ethics at the time. Aaron was exactly the type of academic researcher that MIT meant to have downloading articles from the JSTOR database over its open network. Aaron’s past research in this regard was the basis of a Stanford Law Review Article where he found troubling connections between corporations and their funding of legal research. Source: Stanford Law Review
http://www.stanfordlawreview.org/print/article/punitive-damages-remunerated-research-and-legal-profession
FACT: Aaron wasn’t even violating JSTOR’s Terms of Service at the time. JSTOR and MIT had contractual agreements allowing unlimited downloads to any computers on MITs network.
Source: Alex Stamos, http://unhandled.com/2013/01/12/the-truth-about-aaron-swartzs-crime/
FACT: Downloading JSTOR articles was one minor footnote among the many amazing projects Aaron was working on at the time. From the fall of 2010 until his death in 2013, Aaron’s projects included, but were not limited to: SecureDrop, the leak-protecting technology for journalists now implemented by outlets ranging from The New Yorker to Forbes to The Guardian; the SOPA/PIPA fight, The Flaming Sword of Justice (now The Good Fight), a podcast about activism which went on to reach the top of the iTunes charts; VictoryKit, an online campaigning toolset still mobilizing activists around the world; and co-founding Demand Progress.
Republished from 2014
By Dan Purcell for BoingBoing.
You might ask, like I did, what Aaron’s actions had to do with “computer crimes.” Aaron hadn’t broken into a secure network and stolen credit card numbers. He hadn’t stolen anyone’s healthcare data. He hadn’t violated anyone’s privacy. He hadn’t caused anybody to lose any money. There are things that are “computer crimes” that we all recognize are invasive and dangerous, and this was not one of them.
But Steve Heymann did what bureaucrats and functionaries often choose to do. He wanted make a big case to justify his existence and justify his budget. The casualties be damned.
..He had the Computer Fraud and Abuse Act, which is an over broad federal statute that has been made more broad by federal prosecutors trying to stretch its terms. But under the indictment in Aaron’s case, the government still had to prove that Aaron had gained unauthorized access to a computer system. Our defense was really pretty simple. There were going to be other nuances, and we were going to talk a lot about Aaron’s motivations and the type of person Aaron was, but our bottom line was going to be that Aaron had done only what MIT permitted him to do. He hadn’t gained unauthorized access to anything. He had gained access to JSTOR with full authorization from MIT. Just like anyone in the jury pool, anyone reading Boing Boing, or anyone in the country could have done.
We hoped that the jury would understand that and would acquit Aaron, and it quickly became obvious to us that there really wasn’t going to be opportunity to resolve the case short of trial because Steve Heymann was unreasonable.
Of course, after Aaron’s passing, it’s really easy for them to say “35 years. That was a bluff. It was never gonna happen.” That was not what they were telling us. Heymann always insisted on a sentence of hard time in Federal Prison. We said, “this is really a very trivial thing. Can’t we resolve it with probation or some other thing that made a little more sense and would make it possible for Aaron to go on with his life?”
He said “no.” He insisted that Aaron plead to a felony and serve prison time. And of course, what he said, as prosecutors often do, is that if we go to trial, it won’t be so easy, and if we lose, well, this is a tough judge, and the prosecution is going to recommend a very difficult sentence. Aaron may end up having a term of years.
Imagine how incredible this must have been; the first time someone “transformed” one object into another, like magic, with editing! :-)
A bat transforms into Mephistopheles in ‘The Devil’s Castle’ (1896) Considered the First Vampire Movie, directed by Georges Méliès pic.twitter.com/AHf0tgvcpC
— 41 Strange (@41Strange) August 26, 2017
 The Internet Archive is hosting the Fifth Annual Aaron Swartz Day International Hackathon and Evening Event:
The Internet Archive is hosting the Fifth Annual Aaron Swartz Day International Hackathon and Evening Event:
Location: Internet Archive, 300 Funston Ave, San Francisco, CA 94118
November 4, 2017, from 6:00-7:00 (Reception) 7:30pm – 9:30 pm (Speakers)
The purpose of the evening event, as always, is to inspire direct action toward improving the world. Everyone has been asked to speak about whatever they feel is most important.
The event will take place following this year’s San Francisco Aaron Swartz International Hackathon, which is going on Saturday, November 4, from 10-6 and Sunday, November 5, from 11am-6pm at the Internet Archive.
Hackathon Reception: 6:00pm-7:00pm – (A paid ticket for the evening event also gets you in to the Hackathon Reception.)
Come talk to the speakers and the rest of the Aaron Swartz Day community, and join us in celebrating many incredible things that we’ve accomplished by this year! (Although there is still much work to be done.)
We will toast to the launch of the Pursuance Project (an open source, end-to-end encrypted Project Management suite, envisioned by Barrett Brown and brought to life by Steve Phillips).
Migrate your way upstairs: 7:00-7:30pm – The speakers are starting early, at 7:30pm this year – and we are also providing a stretch break at 8:15pm – and for those to come in that might have arrived late.
Speakers upstairs begin at 7:30 pm.
Speakers in reverse order:
Chelsea Manning (Network Security Expert, Former Intelligence Analyst)
Lisa Rein (Chelsea Manning’s Archivist, Co-founder Creative Commons, Co-founder Aaron Swartz Day)
Daniel Rigmaiden (Transparency Advocate)
Barrett Brown (Journalist, Activist, Founder of the Pursuance Project) (via SKYPE)
Jason Leopold (Senior Investigative Reporter, Buzzfeed News)
Jennifer Helsby (Lead Developer, SecureDrop, Freedom of the Press Foundation)
Cindy Cohn (Executive Director, Electronic Frontier Foundation)
Gabriella Coleman (Hacker Anthropologist, Author, Researcher, Educator)
Caroline Sinders (Designer/Researcher, Wikimedia Foundation, Creative Dissent Fellow, YBCA)
Brewster Kahle (Co-founder and Digital Librarian, Internet Archive, Co-founder Aaron Swartz Day)
Steve Phillips (Project Manager, Pursuance)
Mek Karpeles (Citizen of the World, Internet Archive)
Brenton Cheng (Senior Engineer, Open Library, Internet Archive)
About the Speakers (speaker bios are at the bottom of this invite):
Chelsea Manning – Network Security Expert, Transparency Advocate
Chelsea E. Manning is a network security expert, whistleblower, and former U.S. Army intelligence analyst. While serving 7 years of an unprecedented 35 year sentence for a high-profile leak of government documents, she became a prominent and vocal advocate for government transparency and transgender rights, both on Twitter and through her op-ed columns for The Guardian and The New York Times. She currently lives in the Washington, D.C. area, where she writes about technology, artificial intelligence, and human rights.
Lisa Rein – Chelsea Manning’s Archivist, Co-founder, Aaron Swartz Day & Creative Commons
Lisa Rein is Chelsea Manning’s archivist, and ran her @xychelsea Twitter account from December 2015 – May 2017. She is a co-founder of Creative Commons, where she worked with Aaron Swartz on its technical specification, when he was only 15. She is a writer, musician and technology consultant, and lectures for San Francisco State University’s BECA department. Lisa is the Digital Librarian for the Dr. Timothy Leary Futique Trust.
Daniel Rigmaiden – Transparency Advocate
Daniel Rigmaiden became a government transparency advocate after U.S. law enforcement used a secret cell phone surveillance device to locate him inside his home. The device, often called a “Stingray,” simulates a cell tower and tricks cell phones into connecting to a law enforcement controlled cellular network used to identify, locate, and sometimes collect the communications content of cell phone users. Before Rigmaiden brought Stingrays into the public spotlight in 2011, law enforcement concealed use of the device from judges, defense attorneys and defendants, and would typically not obtain a proper warrant before deploying the device.
Barrett Brown – Journalist, Activist, and Founder of the Pursuance Project
Barrett Brown is a writer and anarchist activist. His work has appeared in Vanity Fair, the Guardian, The Intercept, Huffington Post, New York Press, Skeptic, The Daily Beast, al-Jazeera, and dozens of other outlets. In 2009 he founded Project PM, a distributed think-tank, which was later re-purposed to oversee a crowd-sourced investigation into the private espionage industry and the intelligence community at large via e-mails stolen from federal contractors and other sources. In 2011 and 2012 he worked with Anonymous on campaigns involving the Tunisian revolution, government misconduct, and other issues. In mid-2012 he was arrested and later sentenced to four years in federal prison on charges stemming from his investigations and work with Anonymous. While imprisoned, he won the National Magazine Award for his column, The Barrett Brown Review of Arts and Letters and Prison. Upon his release, in late 2016, he began work on the Pursuance System, a platform for mass civic engagement and coordinated opposition. His third book, a memoir/manifesto, will be released in 2018 by Farrar, Strauss, and Giroux.
Jason Leopold, Senior Investigative Reporter, Buzzfeed News
Jason Leopold is an Emmy-nominated investigative reporter on the BuzzFeed News Investigative Team. Leopold’s reporting and aggressive use of the Freedom of Information Act has been profiled by dozens of media outlets, including a 2015 front-page story in The New York Times. Politico referred to Leopold in 2015 as “perhaps the most prolific Freedom of Information requester.” That year, Leopold, dubbed a ‘FOIA terrorist’ by the US government testified before Congress about FOIA (PDF) (Video). In 2016, Leopold was awarded the FOI award from Investigative Reporters & Editors and was inducted into the National Freedom of Information Hall of Fame by the Newseum Institute and the First Amendment Center.
Jennifer Helsby, Lead Developer, SecureDrop (Freedom of the Press Foundation)
Jennifer is Lead Developer of SecureDrop. Prior to joining FPF, she was a postdoctoral researcher at the Center for Data Science and Public Policy at the University of Chicago, where she worked on applying machine learning methods to problems in public policy. Jennifer is also the CTO and co-founder of Lucy Parsons Labs, a non-profit that focuses on police accountability and surveillance oversight. In a former life, she studied the large scale structure of the universe, and received her Ph.D. in astrophysics from the University of Chicago in 2015.
Cindy Cohn – Executive Director, Electronic Frontier Foundation (EFF)
Cindy Cohn is the Executive Director of the Electronic Frontier Foundation. From 2000-2015 she served as EFF’s Legal Director as well as its General Counsel.The National Law Journal named Ms. Cohn one of 100 most influential lawyers in America in 2013, noting: “[I]f Big Brother is watching, he better look out for Cindy Cohn.”
Gabriella Coleman – Hacker Anthropologist, Author, Researcher, Educator
Gabriella (Biella) Coleman holds the Wolfe Chair in Scientific and Technological Literacy at McGill University. Trained as an anthropologist, her scholarship explores the politics and cultures of hacking, with a focus on the sociopolitical implications of the free software movement and the digital protest ensemble Anonymous. She has authored two books, Coding Freedom: The Ethics and Aesthetics of Hacking (Princeton University Press, 2012) and Hacker, Hoaxer, Whistleblower, Spy: The Many Faces of Anonymous (Verso, 2014).
Caroline Sinders – Researcher/Designer, Wikimedia Foundation
Caroline Sinders is a machine learning designer/user researcher, artist. For the past few years, she has been focusing on the intersections of natural language processing, artificial intelligence, abuse, online harassment and politics in digital, conversational spaces. Caroline is a designer and researcher at the Wikimedia Foundation, and a Creative Dissent fellow with YBCA. She holds a masters from New York University’s Interactive Telecommunications Program from New York University.
Brewster Kahle, Founder & Digital Librarian, Internet Archive
Brewster Kahle has spent his career intent on a singular focus: providing Universal Access to All Knowledge. He is the founder and Digital Librarian of the Internet Archive, which now preserves 20 petabytes of data – the books, Web pages, music, television, and software of our cultural heritage, working with more than 400 library and university partners to create a digital library, accessible to all.
Steve Phillips, Project Manager, Pursuance Project
Steve Phillips is a programmer, philosopher, and cypherpunk, and is currently the Project Manager of Barrett Brown’s Pursuance Project. In 2010, after double-majoring in mathematics and philosophy at UC Santa Barbara, Steve co-founded Santa Barbara Hackerspace. In 2012, in response to his concerns over rumored mass surveillance, he created his first secure application, Cloakcast. And in 2015, he spoke at the DEF CON hacker conference, where he presented CrypTag. Steve has written over 1,000,000 words of philosophy culminating in a new philosophical methodology, Executable Philosophy.
Mek Karpeles, Citizen of the World, Internet Archive
Mek is a citizen of the world at the Internet Archive. His life mission is to organize a living map of the world’s knowledge. With it, he aspires to empower every person to overcome oppression, find and create opportunity, and reach their fullest potential to do good. Mek’s favorite media includes non-fiction books and academic journals — tools to educate the future — which he proudly helps make available through his work on Open Library.
Brenton Cheng, Senior Engineer, Open Library, Internet Archive
Brenton Cheng is a technology-wielding explorer, inventor, and systems thinker. He spearheads the technical and product development of Open Library and the user-facing Archive.org website. He is also an adjunct professor in the Performing Arts & Social Justice department at University of San Francisco.
For more information, contact:
Lisa Rein, Co-founder, Aaron Swartz Day
lisa@lisarein.com
http://www.aaronswartzday.org