Audio Clip:
Link to video of Brewster’s talk (Direct link to Brewster’s talk from within the complete video of all speakers from the event.)
The transcript below has been edited slightly for readability.
Complete transcription:
Welcome to the Internet Archive. I’m Brewster Kahle, Founder and Digital Librarian here, and welcome to our home.
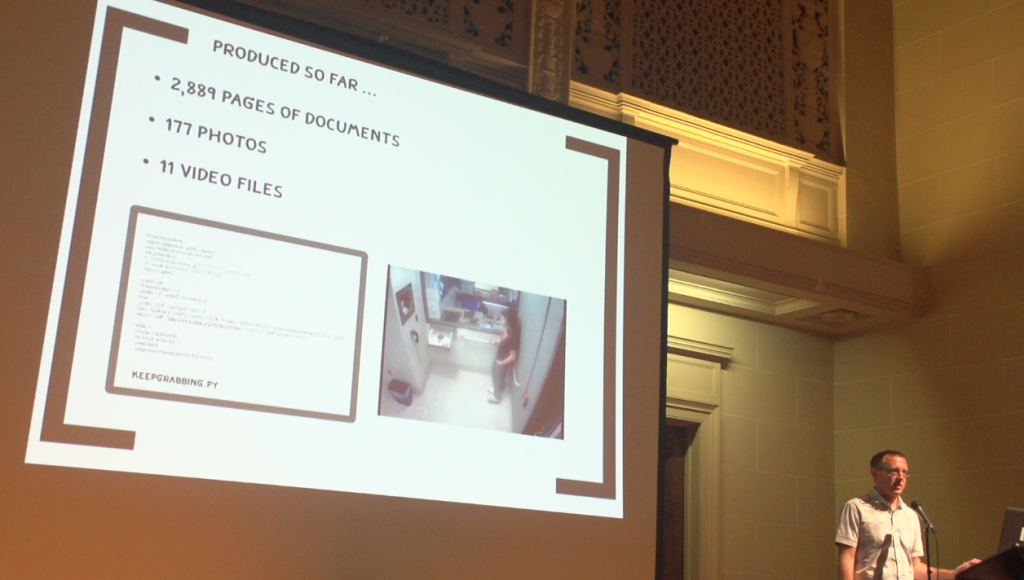
For those that haven’t been here before… The little blinking lights on the 5 petabytes of servers that are in the back, are actually serving millions of people a day, and being kind of a digital library. The little sculptures around are people who have worked at the Internet Archive, including one of Aaron Swartz up toward the front. In the front because he was the architect and lead builder of OpenLibrary.org, which is an Internet Archive site. And also worked on putting Pacer into the Internet Archive (RECAP), Google Books public domain books, and other projects that we’ve worked on over the years. So with this, we’d like to say, “Happy Birthday Aaron, we miss you.”
I’m going to talk about a cheery subject: Plea Bargaining and Torture. When I was trying to think through the approach that was used to bring down Aaron Swartz and to try to make a symbol out of him, I typed these words into my favorite search engine (“Plea Bargaining and Torture) and back came a paper on the subject, that I am going to summarize and also elaborate on.
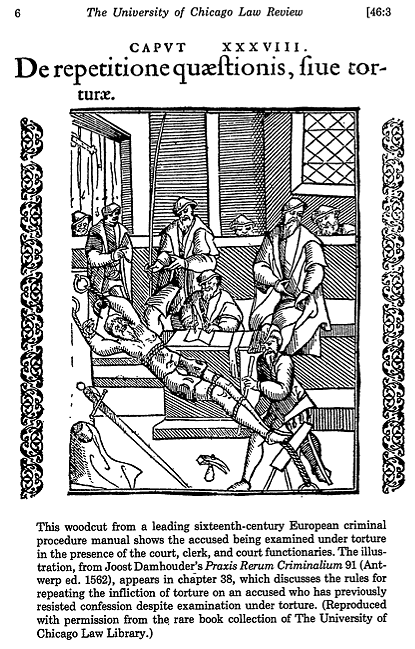
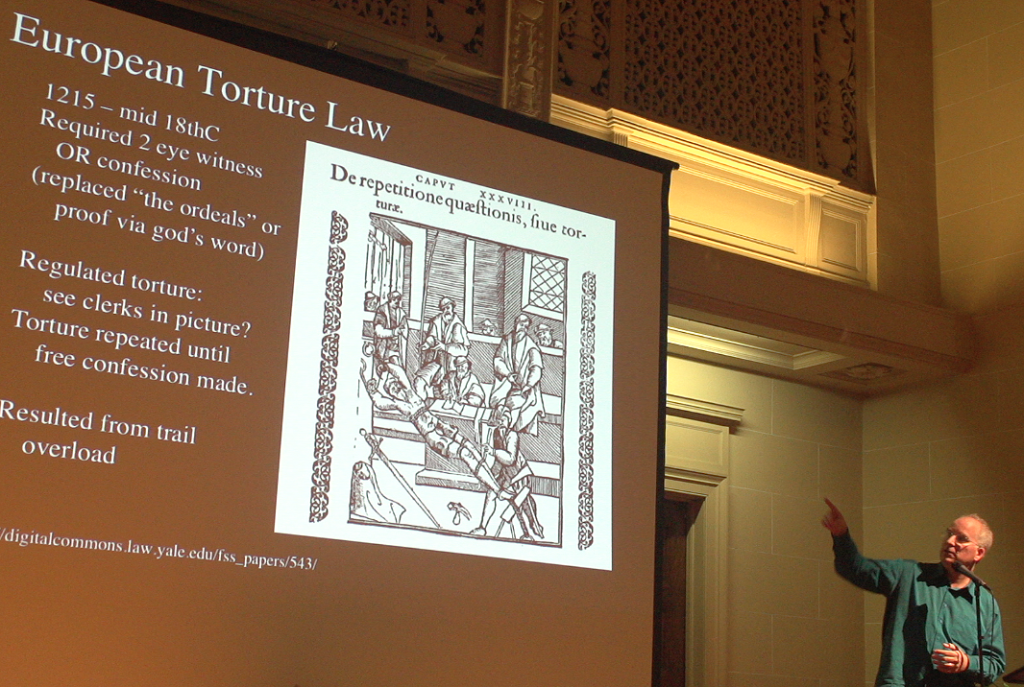
I found this wonderful paper, by a Yale Law Professor, in 1978, comparing European Torture Law and current Plea Bargaining. This might sound a little bit far fetched, but stick with me for a minute.
European Torture Law, I had no idea, was actually a regulated, implemented, part of their court system. It started in 1215, when they stopped going and saying “you’re guilty because God said so.” They had to come up with something else. So they basically had to come up with something that was *that sure.* And they said you either had to have two eyewitnesses, or, you had to confess. And this was actually an unworkable system. And instead of changing that, they tried to force confessions, and they had a whole system for how to do it. They had basically how much regulation, how much leg clamping you had. How many minutes of this, for different crimes.
So you can see in this diagram, and you can see this guy getting tortured here, but he is surrounded by court clerks. So, it’s not this, sort of, the Spanish Inquisition, as Monty Python would have it. This was actually a smart people state-sponsored system that was trying to fix a bug in their court system, in that it was too hard to convict people. So they tortured them into confessions.
Sound familiar?
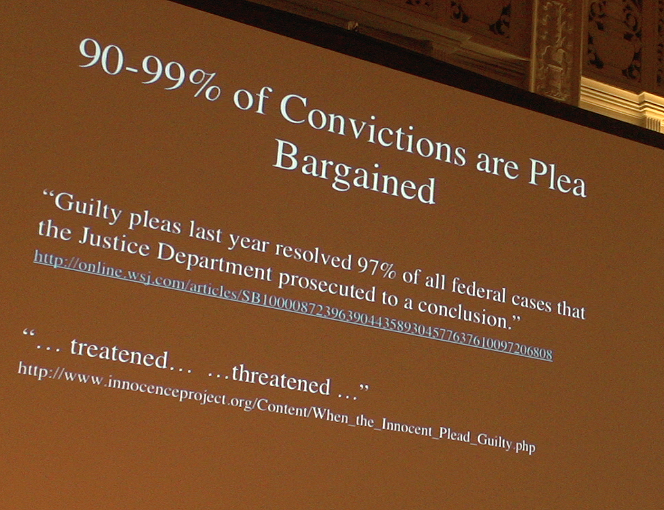
So, in the United States, now, we have between 90 and 99 percent. It depends whether you are in Federal or State court, or which county you’re in. 97% of all convictions at the Federal level are done with plea bargaining.
So you have basically no chance of having a jury before your peers. This is basically a threat system. They actually did studies in Florida where they jacked up the sentences, and the number of people that plea bargained went up. It’s a system to handle convictions outside of the Court System. Outside of the Jury System. Unfortunately, our Constitution actually has something to say about this that’s in pretty direct contradiction:
“The Trial of all Crimes, except in Cases of Impeachment, shall be by Jury;…”
– Article III.2 U.S. Constitution (http://www.archives.gov/exhibits/charters/constitution_transcript.html)
But as another thinker on this has said, basically Plea Bargains have made jury trials obsolete.
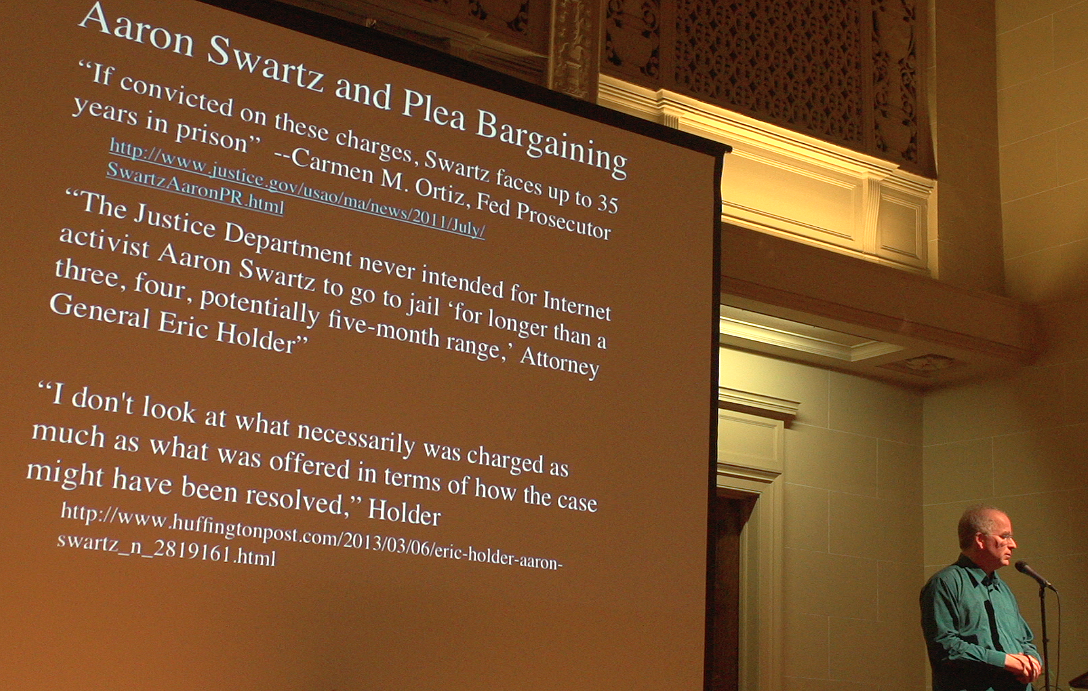
When Aaron Swartz was threatened with 35 years, it’s got to have hit a young, idealistic person pretty hard. 35 years for downloading books too fast from the library? This doesn’t make any sense. Yet that’s a pretty big threat, and may have had something to do with it. When this sort of played out, after his death, I just found that these quotations notable enough that I’m going to sort of, bore you, with putting them up.
So he was faced with 35 years, thanks to Carmen Ortiz. Wonderful. And the Justice Department had never intended for this. No more than a three, four, or potentially five-month range,” said the top attorney in the United States. And we shouldn’t really judge what the prosecutors were doing, based on what they threatened him (with), just by what they were going to do if he pled guilty.
So I think we’ve got a real problem with this. So what’s to do?
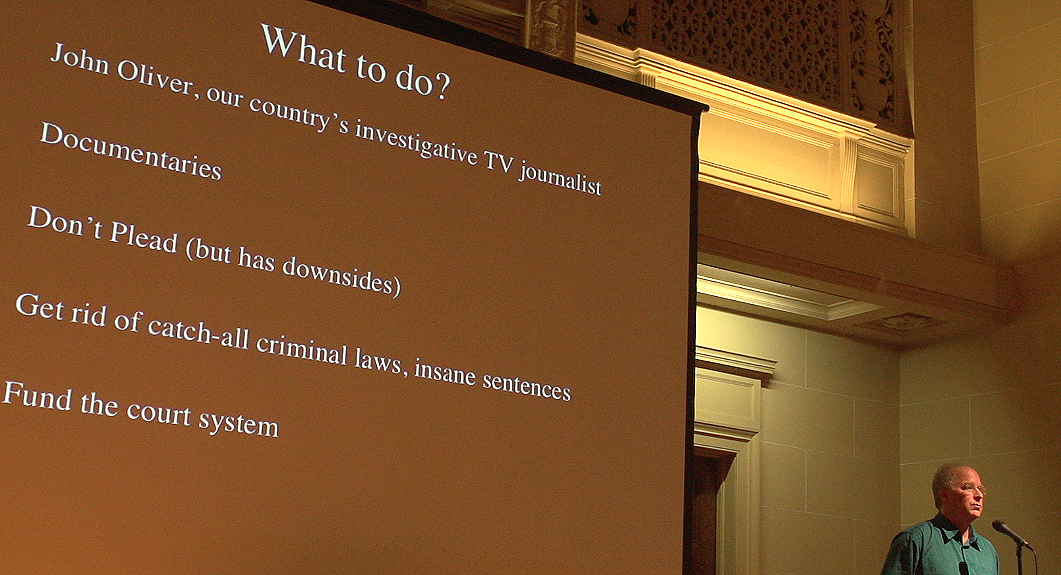
Well, I say we should make some noise about it. I think some of the reasons that we don’t make noise about it is it doesn’t happen to our friends. This sort of thing happens to a lot of “other people.” But, in this case, it did happen to our friend, and I think that it’s important for us to respond to it.
I think John Oliver has been on a roll, in terms of some of these unbelievable sorts of diatribes of going and actually doing research and bringing it in front of people in an interesting way. I’d also like to pitch: “is there a documentarian in the house, say?” That we should go, and really go and put this type of behavior in front of more people.
There are others that are trying by not pleading, but it has its downsides. Basically, gum up the courts. At least for me, I take off my… I don’t go through the surveillance device in the airports, and yes it gums them up a little bit, and I feel like that’s my part to help. Would I actually, if it came right down to it, not plead? To help move this forward? I don’t know. By enlarge, we’ve got ridiculous catch-all laws, and we’ve got sentences that are just outrageous, and these have just got to come under control, as well as let’s actually hire some judges.